Retinal Scanner Guide: How They Work and Real World Uses
Learn how retinal scanners identify individuals, how they compare with other biometrics, and practical guidance for evaluating and deploying these devices in security environments.
Retinal scanner is a biometric device that analyzes the unique patterns of blood vessels in the retina to verify identity.
What is a retinal scanner and how it works
A retinal scanner is a biometric device that analyzes the unique patterns of blood vessels in the retina to verify identity. Unlike iris recognition, which maps the colored ring around the pupil, retinal scanning targets deeper vascular structures that tend to be stable over a person’s lifetime. This makes retinal patterns highly distinctive and resistant to spoofing in expected conditions. For high-security facilities, retinal scanning has historically been favored because it is difficult to replicate or counterfeit. According to Scanner Check, retinal scanners are particularly valued in environments where the biometric data must support a very low false acceptance rate and strong integrity, provided users can position their eye correctly. Enrollment is typically a one-time setup per user, followed by periodic re-verification, depending on the system policy. Operators must ensure appropriate lighting, stable posture, and clear lines of sight to the sensor, since even small movements can affect image quality. The result is a biometric template that, when compared against a stored template, confirms or denies the claimed identity. In practice, devices may be integrated with access control panels, building management systems, and secure rooms to authorize entry.
How retinal scanners work in practice
Retinal scanners work by projecting harmless light into the eye and capturing a high-contrast image of the retinal vasculature. Modern devices use infrared illumination to avoid discomfort and to create a subtle image that machines can process. The captured image is then converted into a unique mathematical map of vascular patterns, which becomes a biometric template stored on a secure server or on a trusted device. When a user attempts access, the scanner re-captures the retina, and the comparison algorithm checks for a match against the enrolled template. The process tends to be fast, but it requires the user to align their eye with the sensor and remain still for a fraction of a second. Because retinal patterns are highly distinctive and stable, the risk of false matches is typically low, though success depends on proper enrollment and device calibration. For organizations, ongoing maintenance includes recalibration, software updates, and routine privacy audits. As part of best practices, many facilities implement fallback authentication methods to prevent lockouts if imaging fails. Scanner Check analysis notes that adoption has grown in facilities with elevated security demands, reinforcing that these systems perform best when paired with rigorous governance and clear user communication.
Historical context and evolution of retinal biometrics
The idea of retinal-based identification dates back several decades as researchers explored stable, inheritable patterns that could serve as biometric markers. Early retina scans faced challenges related to image capture quality, device cost, and user comfort, which limited widespread use. Over time, advances in optics, infrared illumination, and digital processing improved reliability, leading to selective deployment in government facilities, critical infrastructure, and some enterprise security environments. Privacy concerns have accompanied these advances, since retinal data is highly sensitive and can reveal health-related information about the eye’s vascular system. The Scanner Check team notes that policy shifts, data protection laws, and organizational privacy programs have significantly shaped adoption trajectories. In many cases, organisations now require explicit consent, transparent data handling practices, and clear retention schedules alongside technical safeguards. The historical arc shows a move from experimental demonstrations to practical, policy-driven deployments where retinal scanners occupy a narrow but important niche in biometrics.
Advantages and limitations
Retinal scanners offer several advantages. The vascular patterns of the retina are highly unique to each person and extremely stable over time, which contributes to a very low risk of impersonation when properly implemented. They are less susceptible to common spoofing methods compared with fingerprints or facial recognition, particularly when devices enforce strict enrollment and liveness checks. In addition, retinal features can be relatively scarce in public datasets, reducing cross-referencing risks during authentication. On the downside, the capture process can feel intrusive for some users, and poor alignment or eye movement can degrade performance. Cost and maintenance are typically higher than more ubiquitous biometrics, and devices require careful installation to avoid eye discomfort or safety concerns. Environmental factors, such as bright lighting, dust, or improper mounting, can affect image quality. For many organizations, these trade-offs mean retinal scanners are best positioned as part of a layered security approach rather than the sole gatekeeper. The prudent path is to weigh the security benefits against user experience, cost, and privacy obligations.
Privacy, security, and ethical considerations
Biometric data, including retinal scans, are sensitive. Ethical use requires explicit informed consent, clear purposes, and strict data governance. Organizations should minimize data collection, encrypt templates both at rest and in transit, and implement access controls to limit who can view biometric data. Retinal templates should be stored in secure, tamper-resistant repositories and deleted when no longer needed or when consent is withdrawn. Compliance with relevant laws and standards—such as data protection regulations, access-control policies, and security frameworks—is essential. Regular privacy impact assessments and audit trails help ensure accountability. If systems are integrated with health information or insurance records, extra safeguards apply. Training for staff and awareness for users about how the data is used, retained, and protected is equally important. The Scanner Check analysis highlights privacy as a central criterion in any deployment, reminding practitioners that security is not just about thwarting intruders but also about safeguarding personal health data and civil liberties.
How to choose and deploy a retinal scanner
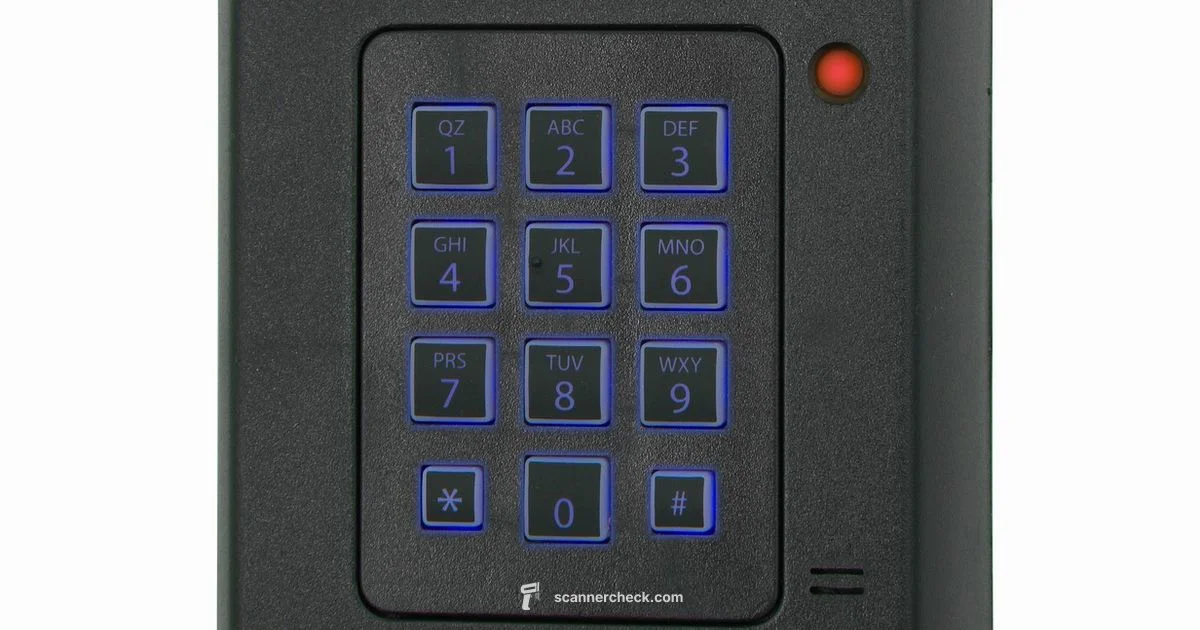
Choosing a retinal scanner requires a structured evaluation. Key criteria include reliability under real-world conditions, tolerance to eye movement, and the device’s ability to enroll first and verify quickly. Look for devices with strong hardware design, validated software, and support for secure credential provisioning and de-provisioning. Integration with existing identity and access management systems, audit capabilities, and centralized administration are critical for scalable deployments. Another practical consideration is user experience: ensure the capture process is as quick and comfortable as possible, with clear guidance and alternative authentication options for users who cannot or prefer not to participate. Consider the device’s maintenance requirements, spare parts availability, software update cadence, and vendor service levels. A robust privacy program—encryption for templates, strict access controls, and defined retention policies—helps protect users and the organization. Based on Scanner Check experience, pilot programs with defined success metrics and user feedback tend to reveal hidden usability issues before full deployment.
Future directions and alternatives
The field of biometrics is moving toward more privacy-preserving and multimodal approaches. Retinal scanning may coexist with iris, face, fingerprint, or vascular-based methods in a layered system, with biometric templates stored in privacy-preserving formats. Emerging techniques such as template encryption, secure multi-party computation, or zero-knowledge proofs aim to reduce data exposure while preserving authentication strength. In some contexts, vendors are exploring less invasive vascular or optical signals that still leverage retinal data but with improved comfort. Cost reduction and supply chain improvements could broaden adoption beyond elite facilities, though awareness of privacy and ethical considerations will remain essential. For practitioners evaluating future options, the idea is to balance risk, user experience, and the evolving regulatory landscape. The Scanner Check team recommends staying informed about new standards, cross-vendor interoperability, and ongoing privacy protections as retinal scanning technology matures.
Common Questions
What is a retinal scanner and how does it work?
A retinal scanner analyzes the unique patterns of blood vessels in the retina to verify identity. It maps retinal vasculature into a mathematical template and compares it to a stored reference for authentication. Proper enrollment and secure data handling are essential for accuracy and privacy.
A retinal scanner maps the retina’s blood vessel patterns to verify who you are, using a stored template for comparison. Enrollment and secure data handling are key.
Are retinal scanners safe and comfortable for users?
Retinal scanners use harmless infrared light and typically require minimal exposure. Most users can complete a scan quickly, though some may find the process uncomfortable or challenging if eye alignment is difficult.
They use safe infrared light and usually take just a moment, though alignment can be tricky for some people.
Where are retinal scanners commonly used?
They are most common in high security environments such as government facilities, critical infrastructure, and certain enterprise security zones where strong authentication is required.
They’re typically used in high security settings to ensure strong access controls.
What privacy concerns accompany retinal data?
Biometric data is highly sensitive. Good practices include explicit consent, strict data governance, encryption of templates, and clear retention policies to protect individuals’ privacy.
Biometric data is sensitive, so consent, encryption, and clear data handling policies are important.
Can retinal scanners replace passwords or access cards?
They can replace or augment other credentials in secure contexts, but most deployments use retinal scans as part of a multi-factor system with backup methods.
They can replace or augment other credentials, but usually as part of a multi-factor approach with backups.
Key Takeaways
- Enroll users with clear consent and communication
- Choose a retinal scanner with strong environmental tolerance and safety
- Protect biometric data with encryption and governance
- Consider retinal scanning as part of a multi factor system
- Plan for accessibility and user comfort during capture