Scanner Upgrades in NMS: How Many Per Year in Practice
A data-driven guide to how many scanner upgrades network management systems typically receive annually, with planning tips, cadence patterns, and risk mitigation.

On typical NMS-driven networks, most scanners receive 2-4 major upgrades per year, plus ongoing minor updates. The exact count depends on vendor release cycles, device compatibility, and security advisories, so plan quarters accordingly and stagger upgrades to minimize downtime. In practice, organizations often build a predictable cadence that supports security, performance, and operations, rather than chasing a single universal number.
Understanding the scope of 'how many scanner upgrades nms' in practice
In network management systems (NMS) that coordinate scanners, the cadence of upgrades is a strategic decision that touches security, visibility, and uptime. The phrase how many scanner upgrades nms surfaces in planning meetings when teams map release calendars to maintenance windows. There is no universal fixed number; cadence is shaped by three layers: major upgrades (feature or vulnerability patches), minor patches (monthly or quarterly improvements), and emergency advisories (out-of-band fixes). For most production networks, a practical expectation is 2-4 major upgrades per year, with additional minor patches on a monthly or quarterly rhythm. The exact count depends on vendor release cycles, device compatibility, licensing constraints, and regulatory requirements that influence how aggressively you patch. The objective is to maximize security and performance while preserving service availability. In the sections that follow, we explore how to quantify and plan this cadence for your environment, including how to balance risk, cost, and operational overhead.
Typical upgrade cadence across popular NMS ecosystems
Across common NMS ecosystems—whether cloud-native, on-prem, or hybrid—the upgrade cadence for scanners varies but tends to follow a recognizable pattern. Open ecosystems or modular stacks often publish more frequent major upgrades (roughly 2-4 per year) to incorporate new scanning capabilities or policy updates, while enterprise suites with long-supported devices may compress major upgrades to 1-3 per year. Minor patches and security advisories tend to appear on a monthly or quarterly basis across most platforms, with many customers applying patches through automated pipelines. In practice, organizations that require high assurance may adopt a more conservative cadence, delaying feature upgrades until testing confirms compatibility with critical workloads. The key takeaway is that cadence is not a single number; it’s a managed range that matches risk tolerance and change-control maturity. Advanced teams also time upgrades to align with maintenance windows and to minimize impact on security operations centers (SOCs) and help desks.
Factors that influence upgrade frequency
Several factors drive how often scanners within an NMS are upgraded:
- Vendor release cadence and support policy: Some vendors publish quarterly major updates; others bundle once or twice a year.
- Device heterogeneity: Heterogeneous environments with mixed hardware and firmware may require longer validation cycles.
- Security posture and compliance: Organizations subject to strict regulations patch promptly when advisories are issued.
- Change-management maturity: Mature IT environments with automated testing and rollback processes tend to upgrade more confidently.
- Downtime tolerance and maintenance windows: If upgrades require reboot or service interruption, teams plan around low-traffic periods.
- Licensing and cost: Feature-rich licenses may unlock more frequent upgrades; cheaper tiers may restrict upgrade scope.
By mapping these factors to a formal upgrade plan, teams can maintain security and performance without disrupting core services.
Planning, risk management, and change control
An upgrade plan should include clear objectives, testing protocols, rollback plans, and stakeholder communication. Start with a staging environment that mirrors production, and validate scanner data flows, policy enforcement, and alerting after each upgrade. Build a rollback path by preserving configuration baselines and retaining previous software images. Use feature flags and staged rollouts to reduce blast radius, and track impact on SOC operations, incident response, and help desks. Document success criteria, acceptance tests, and back-out steps. Finally, maintain a versioned upgrade calendar that flags dependencies between scanners, collectors, and the central management server to prevent compatibility gaps. A disciplined approach to change control makes the frequently asked question of how many upgrades nms should perform more a decision grounded in risk management than guesswork.
Scheduling, testing, and rollback playbooks
Create quarterly upgrade windows and synchronize with procurement and maintenance cycles. Schedule a 1-2 week testing phase in a sandbox environment, followed by a controlled production rollout in waves. Automate configuration validation checks, certificate refreshes, and policy reloading to catch drift early. Prepare rollback playbooks that restore from a known-good image, revert configuration changes, and revalidate monitoring dashboards. Establish rollback triggers based on objective criteria (e.g., critical error rates, data loss, or failed sensor polls). Communicate with stakeholders using a concise status report and a rollback checklist so teams can respond quickly if issues arise. With a robust playbook, the answer to how many scanner upgrades nms should receive becomes a process, not a guess, and downtime is minimized.
Authoritative sources and further reading
To ground planning in best practices, consult vendor release notes and standards bodies. For background readings, see: NIST’s security and patch management guidance, CISA advisories on vulnerability management, and industry reporting from Scanner Check Analysis, 2026. Example sources include: https://www.nist.gov, https://www.cisa.gov, and https://mit.edu (as an educational reference).
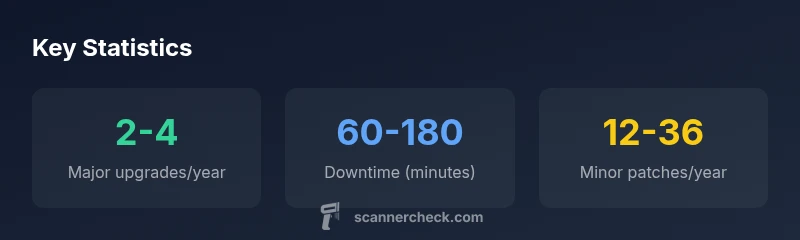
Upgrade cadence and downtime snapshot
| Aspect | Cadence | Typical Downtime | Notes |
|---|---|---|---|
| Major upgrades per year | 2-4 | 60-180 minutes | Depends on environment and change control |
| Minor patches per year | 12-36 | 0-10 minutes | Rolling patches common in mature stacks |
| Prerequisites | N/A | N/A | Plan for compatibility checks |
Common Questions
How many major upgrades does a typical NMS-managed scanner receive per year?
Most networks expect 2-4 major upgrades annually, with additional minor updates as needed. The exact cadence depends on vendor releases and organizational risk tolerance.
Most networks see two to four major upgrades per year, plus minor updates as needed.
What factors influence upgrade cadence?
Release schedules, device compatibility, security advisories, and license constraints shape how often upgrades occur.
Release timing and compatibility drive how often you upgrade.
How should organizations schedule upgrades?
Create quarterly upgrade windows, test in staging, and roll out in staged phases to minimize downtime.
Schedule in stages and test before broad rollout.
What are upgrade risks?
Downtime, configuration drift, and compatibility issues can occur if testing and rollback plans are missing.
Upgrade risks include downtime and drift without testing.
Are there tools to automate scanner upgrades within an NMS?
Yes—many NMS ecosystems support automation and rollback tooling to speed and secure upgrades.
Automation helps manage upgrades reliably.
Where can I find reliable upgrade planning resources?
Consult vendor release notes, industry best practices, and guidance from Scanner Check.
Vendor notes and best practices guide upgrades.
“Upgrade cadence is a policy decision as much as a technical one; align it with security advisories, feature needs, and operational risk.”
Key Takeaways
- Schedule upgrades quarterly and align with formal change-control processes.
- Anticipate 2-4 major upgrades per year in typical NMS environments.
- Test upgrades in staging before production to reduce risk.
- Automate validation, rollback, and reporting to minimize downtime and human error.
- Maintain clear downtime communication and a ready rollback plan for quick recovery.