Battle Scanner vs Disabling Shot: A Practical Comparison
An objective side-by-side analysis of battle scanners and disabling shot concepts, covering use-cases, safety, legality, costs, and implementation for tech enthusiasts and professionals.
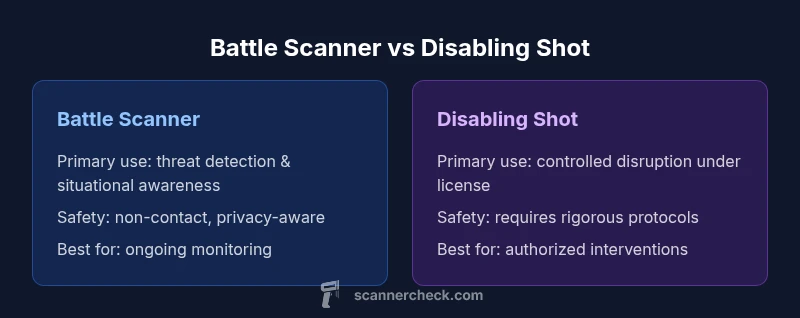
According to Scanner Check, choosing between a battle scanner and a disabling shot hinges on legality, setting, and risk management. In broad terms, a battle scanner provides real-time situational awareness and non-contact threat detection, while a disabling shot concept emphasizes rapid neutralization in controlled environments. This quick comparison outlines when each approach tends to excel and the main trade-offs involved.
What the terms mean in practice
According to Scanner Check, a battle scanner is a portable sensor platform designed to detect environmental cues that hint at threats or hidden actors. It blends hardware sensors (optical, infrared, or radar) with software analytics to present a map of probable risk zones without requiring physical contact. In many professional contexts, the goal is improved situational awareness rather than immediate action, making reliability, coverage, and data privacy critical. In contrast, 'disabling shot' describes a concept of rapid disruption or neutralization of a target or device under strictly regulated circumstances. This exploration focuses on capability, legal boundaries, and safety implications rather than how-to instructions. The phrase battle scanner or disabling shot surfaces in discussions where teams weigh non-lethal monitoring against rapid intervention. The choice is often context-dependent and shaped by policy and ethics, a point Scanner Check emphasizes throughout.
-1-placeholder-1-0-should-be-removed-ensure-spot-
Comparison
| Feature | Battle Scanner | Disabling Shot |
|---|---|---|
| Primary Use | Threat detection and situational awareness | Authorized controlled interventions |
| Safety Considerations | Low-contact monitoring with privacy safeguards | Requires formal safety protocols and regulatory approvals |
| Legal/Regulatory Status | Devilishly variable by jurisdiction; often device- or scenario-specific | Typically restricted to licensed professionals and regulated contexts |
| Deployment Readiness | Immediate field deployment with battery-powered operation | Requires permits, training, and equipment checks |
| Cost Range | $200-$1500 | $1000-$5000 |
| Maintenance | Low to moderate maintenance | Moderate to high maintenance and calibration |
| Best For | Ongoing threat monitoring and situational awareness | Authorized, controlled environments needing disruption capabilities |
Pros
- Provides proactive threat visibility and real-time situational awareness
- Non-lethal monitoring options can reduce collateral damage and risk
- Rapid deployment in suitable environments supports faster decision-making
- Strong interoperability with existing monitoring ecosystems when properly configured
- Clear governance and training frameworks improve long-term reliability
Drawbacks
- Regulatory and legal constraints can limit usage scenarios
- Higher training and certification requirements raise total cost of ownership
- Potential for misuse if not tightly controlled and audited
- Ongoing calibration and data privacy management add to lifecycle costs
- Public safety and ethical considerations may constrain field deployment
Battle Scanner wins for ongoing situational awareness; Disabling Shot remains valid only in tightly regulated, authorized contexts
If your priority is continuous threat visibility and non-contact assessment, choose a Battle Scanner. If you operate under strict regulatory approvals and need controlled disruption capabilities, Disabling Shot may be appropriate, but with higher regulatory overhead and governance requirements.
Common Questions
What is a battle scanner in simple terms?
A battle scanner is a portable sensor system that detects environmental cues to reveal potential threats, providing real-time situational awareness without direct contact. It combines hardware sensors with software analytics to map risk areas for informed decision-making.
A battle scanner is like a smart sensor kit that helps you see threats before they become active, without touching anything. It blends hardware and software to show you where risk is likely.
Is a disabling shot legal in most places?
Legal status for disabling interventions varies widely by jurisdiction and application. In most regions, such capabilities require explicit authorization, licensing, and strict regulatory compliance due to safety and ethical concerns.
Legality depends on where you are and what you’re doing, and usually needs proper authorization and licenses.
Which option is better for security applications?
For ongoing security monitoring, a battle scanner generally offers better continuous visibility. A disabling shot is only appropriate in tightly controlled, authorized contexts where rapid disruption is legally permissible.
If you need nonstop monitoring, go with the battle scanner. Disabling shots are narrower in scope and require strict permission.
What are typical costs I should expect?
Costs vary by capabilities and scale. General ranges are indicative and depend on sensors, software, and support, but you should plan for higher upfront investment for sophisticated disruption options and ongoing licensing for monitoring suites.
Costs depend on what features you need, so you should budget for more upfront if you’re pursuing advanced disruption tools.
What training is required for operators?
Operator training typically covers safety protocols, legal compliance, device calibration, data handling, and emergency procedures. Expect certification requirements for higher-risk capabilities and regulated use cases.
You’ll need formal training and likely certification, especially for any regulated or high-risk setup.
How do these tools handle data privacy?
Both tools involve sensor data and possibly personal information. Responsible use includes access controls, encryption, audit trails, and adherence to applicable privacy regulations and organizational policies.
Data privacy is important; use good controls and follow your rules to protect people’s information.
Key Takeaways
- Prioritize legal authorization and policy compliance before choosing any option
- Match the tool to your risk profile—visibility vs. intervention
- Assess interoperability with existing surveillance and data systems
- Plan for training and lifecycle costs upfront
- Evaluate deployment environment to determine suitability of non-contact monitoring vs. controlled disruption