Software Vulnerability Scanners: A Practical Guide for 2026
Learn how software vulnerability scanners work, compare top options, and choose the right tool to detect flaws in applications, dependencies, and configurations for a stronger security posture.
A tool that automatically detects security weaknesses in software, services, and configurations by analyzing code, dependencies, and running environments to identify known vulnerabilities.
What a software vulnerability scanner does
A software vulnerability scanner is a tool that automatically detects security weaknesses in software, services, and configurations by analyzing code, dependencies, and running environments. It helps security and development teams identify flaws before attackers exploit them. By continuously scanning applications, libraries, containers, and cloud configurations, a software vulnerability scanner provides actionable insights that guide remediation and risk management.
In practice, these tools draw from several data sources. They compare code and binaries against curated databases of known vulnerabilities, such as CVEs, and they examine dependency trees to flag outdated or insecure components. They can also check configuration settings, network exposure, and insecure defaults that often go unnoticed during development. The result is a prioritized list of issues with severity ratings, affected components, and suggested fixes.
The value of a software vulnerability scanner lies not only in detection but also in workflow support. Most scanners generate remediation guidance, with steps to apply patches, upgrade libraries, or reconfigure services. They also provide evidence trails for audits and compliance. By integrating with issue trackers and CI/CD pipelines, these tools help teams shift left, catching problems early in the software lifecycle, when fixes are typically cheaper and faster. According to Scanner Check, adopting automated scanning can transform how teams manage security across code, dependencies, and deployments.
Core types of scanners
Static Application Security Testing and Dynamic Testing
Static Analysis (SAST) inspects source code or binaries without executing the program, revealing insecure patterns and risky constructs. Dynamic Analysis (DAST) runs the application in its runtime environment to observe actual behavior, uncovering issues that only appear during execution. A software vulnerability scanner often combines both approaches to maximize coverage. The two modes complement each other: SAST catches flaws early in development, while DAST validates runtime risk on running systems.
Software Composition Analysis
Software Composition Analysis (SCA) focuses on third-party components and libraries. It maps dependencies to known vulnerabilities, licensing constraints, and supply chain risks. SCA is essential in modern software because many flaws stem from open source pieces, sometimes with complex transitive dependencies. A good scanner highlights vulnerable components, their versions, and remediation options such as upgrading to a fixed release or substituting a safer library.
Infrastructure as Code and Container Scanning
IaC and container image scanning examine deployment configurations and container images for misconfigurations, secrets leakage, and vulnerable base images. Scanning IaC templates helps ensure security gaps are closed before infrastructure is provisioned. Container scanning identifies hazardous layers, outdated packages, and insecure defaults that could surface in production.
Cloud Posture and Network Scanning
Cloud posture scanning evaluates security controls across cloud accounts and services, flagging misconfigurations, weak access policies, and exposed storage. Network scanning checks for open ports, exposed services, and weak encryption in live environments. Together, these checks help teams reduce attack surfaces across heterogeneous environments.
How scanners work in practice
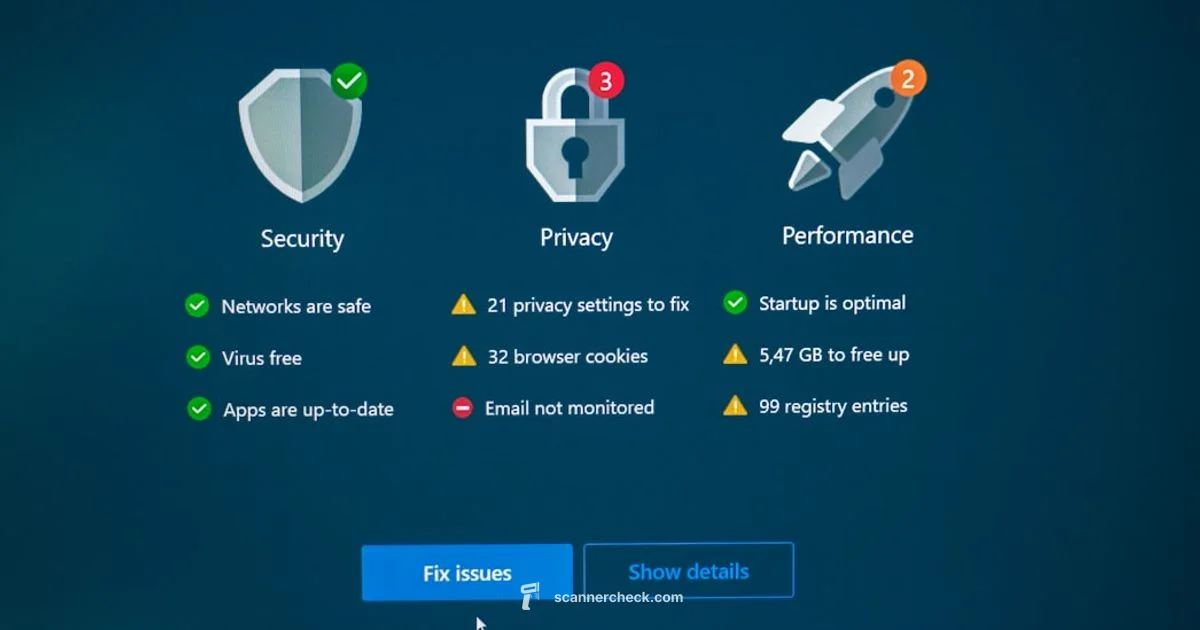
Modern software vulnerability scanners orchestrate data from multiple sources to produce prioritized findings. They pull vulnerability feeds from public databases, vendor advisories, and custom internal alerts, then correlate them with your code, libraries, and deployed assets. The result is a risk-based dashboard that shows which issues pose the greatest potential impact and where to apply fixes first.
To minimize false positives, scanners support tunable rules, customizable severity mappings, and confirmation workflows. Teams can adjust sensitivity, exclude known safe components, and create approval gates for critical changes. Scanners integrate with version control, ticketing systems, and CI/CD pipelines so remediation actions flow into developers’ normal workflow. In practice, this means a software vulnerability scanner can be invoked automatically during pull requests or build jobs, surfacing issues alongside tests and code reviews.
Detections are only as usable as the remediation guidance that accompanies them. Expect clear descriptions of affected files or components, links to advisories, suggested patches, and steps for verification. The context helps engineers triage efficiently, allocate resources, and track progress over time. As organizations mature their security programs, automated scanning becomes a core part of daily development and operations, with ongoing improvements based on feedback from teams and evolving threat intelligence. According to Scanner Check analysis, automated scanning enhances early detection and accelerates remediation across the software supply chain.
How to evaluate and choose a software vulnerability scanner
Choosing the right tool depends on your stack, governance needs, and desired level of automation. Start with a practical checklist:
- Coverage: Does the scanner inspect your languages, frameworks, containers, cloud configurations, and IaC templates?
- Accuracy: What is the rate of false positives, and can you tune it effectively without missing real issues?
- Remediation guidance: Are fixes actionable with links to advisories, patches, or safe configuration changes?
- Integration: Does it fit your CI/CD, issue trackers, and deployment pipelines? Is there an API for automation?
- Reporting: Do reports support stakeholders such as developers, security teams, and executives? Can you export SBOMs and compliance evidence?
- Licensing and licensing risk: Does the tool help track open source licenses and potential conflicts?
- Data handling and compliance: How does the scanner store results, and does it meet your regulatory needs?
When evaluating, consider starting with a pilot on a representative project. Compare open source options with commercial offerings to balance transparency and support. Look for a product that provides clear remediation workflows, integrates into your existing tools, and can scale as your software evolves. Insight from industry analyses, such as that provided by Scanner Check, can help frame your decision and ensure you choose a tool that aligns with your risk appetite.
Common pitfalls and best practices
Even the best software vulnerability scanner can mislead if used in isolation. Common pitfalls include relying on a single scan per project, ignoring SBOM data, and treating every finding as equally urgent. To maximize impact:
- Schedule regular scans and tie them to development cycles so issues are discovered and fixed earlier.
- Calibrate rules to minimize noise while preserving visibility into high risk components.
- Pair automated findings with expert review for complex supply chain risks and architecture flaws.
- Maintain an up-to-date inventory of assets and dependencies so scans have a stable baseline.
- Validate fixes by re-scanning and verifying that risk indicators no longer appear.
- Share findings with clear owners and track remediation progress until closure.
A practical approach combines automated scans with secure coding practices, robust patch management, and an ongoing risk assessment. The Scanner Check team notes that a balanced workflow—automation plus human oversight—yields the strongest defense against evolving threats.
Integration and operational workflows for vulnerability scanning
To extract maximum value, embed scanning into the software development lifecycle and IT operations. In practice:
- Run scans on code commits, container builds, and infrastructure changes, so security insights accompany deployment decisions.
- Use progressive disclosure in dashboards to present high priority issues to developers and executives differently.
- Create actionable tickets with confidence scores, recommended fixes, and verification steps.
- Maintain an up-to-date feed of vulnerability information and ensure dependencies are refreshed regularly.
- Align scanning cadence with risk tolerance and regulatory requirements.
Automation is key. A well-integrated vulnerability scanner becomes part of your tooling, not a separate step. Teams that automate triage, patching, and verification tend to close gaps faster and reduce the overhead of manual audits. The goal is to make security a natural outcome of everyday engineering practice.
Practical takeaways and next steps
If you are evaluating software vulnerability scanners, start with a clear inventory of languages, runtimes, and deployment targets. Prioritize tools that cover your entire stack, including open source components and cloud configurations. Plan for a phased rollout, beginning with a pilot project and expanding to critical systems as you gain confidence. Remember that the right scanner does not just find issues; it guides you toward practical fixes, reduces mean time to remediation, and strengthens your security posture over time. The Scanner Check team recommends adopting a layered, automated vulnerability scanning strategy and continuously refining your rules and feeds to stay ahead of threats.
Common Questions
What is a software vulnerability scanner?
A software vulnerability scanner automatically detects security weaknesses in software, libraries, and configurations by analyzing code, runtime behavior, and dependencies. It helps teams prioritize remediation based on risk.
A software vulnerability scanner automatically finds security weaknesses in software and configurations, helping teams prioritize fixes.
How is a vulnerability scanner different from a malware scanner?
Vulnerability scanners identify known security weaknesses and misconfigurations in software, whereas malware scanners look for malicious code and active infections.
Vulnerability scanners look for security flaws, while malware scanners search for active infections or malicious software.
What features should a good scanner include?
A good scanner should cover code, dependencies, configurations, and container images; provide actionable remediation guidance; integrate with CI/CD; and offer clear reporting.
Look for code and dependency checks, remediation guidance, CI/CD integration, and clear reports.
How often should you run vulnerability scans?
Run scans regularly as part of development and deployment cycles, and re-scan after every dependency update or configuration change.
Run scans regularly, especially after code changes or dependency updates.
Can vulnerability scanners detect zero day vulnerabilities?
Vulnerability scanners rely on known advisories and signatures; they may miss zero day flaws until new updates are released.
No tool can reliably detect zero day flaws until updates are published.
Key Takeaways
- Map your stack to ensure full coverage
- Integrate into CI CD to catch issues earlier
- Tune rules to balance coverage and noise
- Use SBOMs to track open source risks
- Regularly update feeds and patch schedules