Data Security & Vulnerability Scanners
Tools and approaches for network and device vulnerability scanning.
109 articles

AI Scanner Detector: A Practical Guide
Vue scanner software: A Comprehensive Definition and Guide

The Ultimate List of Vulnerability Scanners: Top Picks for 2026
Port Scanner Open and Open Ports Explained

Port Open Scanner: Definition, Tools, and Best Practices

What Is a Port Scanner? Definition, Types, and Uses
Learn what a port scanner is, how it works, and why it matters for network security. Explore types, ethics, and practical tips for safe scanning practices.

Bug Scanner: A Practical Guide to Finding Bugs Early

Vulnerability Scanners Compared: Nessus-like Options

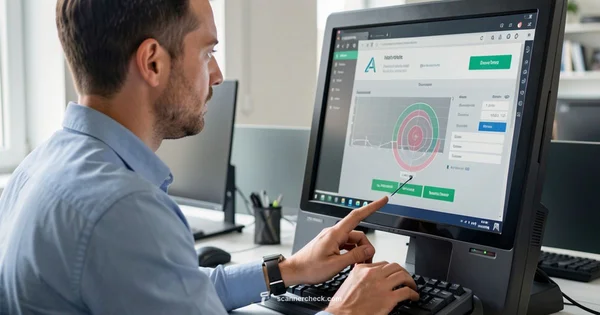
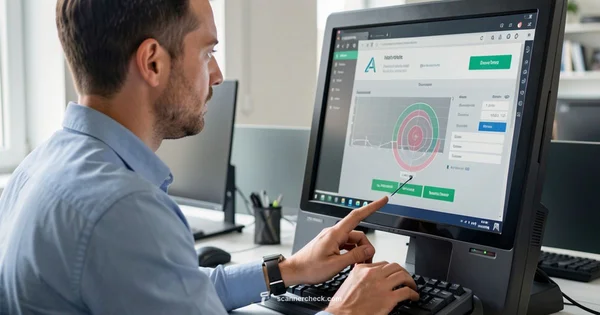
Scanner and Incident Dashboard: An Analytical Comparison for IT Pros
A rigorous, analytic comparison of scanner dashboards versus integrated incident dashboards, with practical guidance for IT teams on selection, integration, and real-time risk monitoring.

The Ultimate List of Vulnerability Scanners: Top Picks for 2026
Port Scanner Open and Open Ports Explained

Port Open Scanner: Definition, Tools, and Best Practices
A practical guide to port open scanners, how they work, and ethical use. Learn definitions, tools, and defense strategies for secure networks.

What Is a Port Scanner? Definition, Types, and Uses

Bug Scanner: A Practical Guide to Finding Bugs Early

Vulnerability Scanners Compared: Nessus-like Options
Objective comparison of vulnerability scanners like Nessus, covering features, deployment options, reporting workflows, and licensing considerations for IT teams deciding which tool best fits their security program.
