Vulnerability Scanners Compared: Nessus-like Options
Objective comparison of vulnerability scanners like Nessus, covering features, deployment options, reporting workflows, and licensing considerations for IT teams deciding which tool best fits their security program.
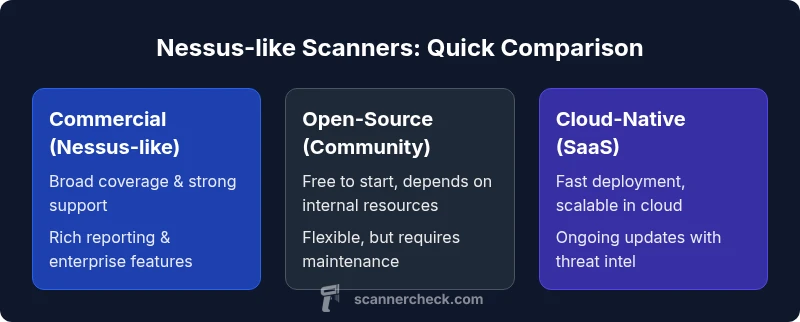
TL;DR: Vulnerability scanners like Nessus are essential for proactive risk management, but the best choice depends on your environment. This comparison highlights three common paths—commercial Nessus-like scanners, open-source alternatives, and cloud-native options—so you can pick based on coverage, ease of use, and reporting needs. For most teams, a hybrid approach that balances depth with speed provides the best ROI.
Why vulnerability scanners matter in modern security programs
A vulnerability scanner like nessus has become a non-negotiable component of modern security programs. It automates asset discovery, detects known weaknesses, and prioritizes remediation tasks for operators and developers. The Scanner Check team emphasizes that the real value comes not from a single scan, but from an ongoing, integrated process that combines scan results with risk decisions, asset context, and remediation workflows. In practice, teams that implement regular, automated scans along with clear owner accountability see faster remediation and better overall risk posture. This section lays the groundwork for evaluating Nessus-like scanners by clarifying what you’re optimizing for: visibility, speed, accuracy, and actionable reporting.
Key terms to know include coverage breadth (hosts, containers, cloud assets), update cadence (plugin or rules updates), and the quality of built-in reporting for executives and security engineers. A mature program uses standardized baselines, schedules scans to align with change windows, and taps into ticketing and asset management systems to close the loop. This approach is supported by industry guidance and, in many cases, by the experience of organizations that have adopted security automation at scale. According to Scanner Check, the most effective strategies combine automated scanning with a well-defined remediation workflow and executive-level risk communication.
In summary, vulnerability scanning is not a one-off task. It’s a continuous discipline that informs risk-based decision-making and drives practical improvements across IT, security operations, and development teams.
Feature Comparison
| Feature | Nessus-like Scanner (Commercial) | Open-Source Alternative (Community Edition) | Cloud-Native Scanner (SaaS) |
|---|---|---|---|
| Coverage | Broad host, network, container, and some cloud asset coverage | Strong host and plugin ecosystem but limited out-of-the-box cloud assets | Cloud-native asset discovery and API coverage; rapid onboarding for cloud environments |
| Detection Depth | High depth with frequent CVE updates and professional support | Good baseline checks; depends on community rules and updates | High depth with cloud-specific checks and automated threat intelligence |
| Update Frequency | Daily to weekly plugin/rule updates | Community-driven cadence; varies by module | Continuous or on-demand updates via cloud service |
| Deployment Model | On-prem or centralized management with agents | Primarily on-prem with community tooling | Fully cloud-based SaaS with web interface |
| Reporting & Dashboards | Rich, customizable reports; enterprise-ready dashboards | Standard reports with potential for customization | Integrated dashboards with analytics and trends in the cloud |
| Pricing Model | Licensing per host or per seat; maintenance included | Open-source (free) but with hidden maintenance costs | Subscription-based with tiered features and usage limits |
| Ease of Use | Mature UI, strong vendor documentation, good onboarding | Steeper learning curve; relies on community support | Intuitive SaaS UI; rapid deployment and scaling |
| Integrations | SIEM, ticketing, CMDB, and security orchestration tools | Limited official integrations; relies on plugins and community scripts | Native integrations with CI/CD, ITSM, and cloud-native tools |
| Compliance Coverage | Broad checks for PCI DSS, HIPAA, and more; documented mappings | Compliance relies on community plugins and configurations | Compliance packs and templates for common frameworks |
| Best For | Large enterprises needing depth, support, and customization | Teams with technical expertise and budget constraints | Organizations seeking fast deployment and scalable cloud coverage |
Pros
- Improved threat visibility through automated, repeatable scans
- Centralized reporting supports audits and management buy-in
- Flexible deployment options (on-prem, cloud, or hybrid)
- Strong ecosystem of plugins/updates in commercial options
- Scalability to large asset inventories and diverse environments
Drawbacks
- Potential for false positives requiring tuning and triage
- Requires ongoing maintenance and governance to stay effective
- Licensing costs can be significant for large environments
- Open-source options may demand more in-house expertise and support
Nessus-like scanners are a solid default for many organizations, especially where depth and vendor support matter.
For teams needing mature features, broad compliance coverage, and strong vendor backing, commercial Nessus-like options usually deliver the most reliable results. Open-source or cloud-native alternatives excel for budget-conscious teams or rapid deployment, but may require more in-house setup and ongoing tuning.
Common Questions
What defines a vulnerability scanner like Nessus, and how does it differ from other security tools?
A vulnerability scanner like Nessus is a specialized tool that automatically discovers security weaknesses across hosts, networks, and apps by checking configurations, patches, and known CVEs. It differs from penetration testing tools by focusing on automated finding and prioritization rather than manual exploitation. It also complements compliance scanners by emphasizing ongoing risk visibility rather than point-in-time checks.
A Nessus-like scanner automatically finds weaknesses across your network and tells you what to fix first, unlike pen tests which try to break in manually.
Can vulnerability scanners detect zero-day vulnerabilities?
Most vulnerability scanners detect known vulnerabilities and misconfigurations based on CVE databases and rule sets. They rarely identify true zero-day exploits unless a new patch or detection rule is released. Regular updates and threat intelligence feeds help, but they are not a substitute for proactive threat hunting.
They mainly catch known issues; zero-days require threat intelligence and specialized analysis beyond standard scanners.
What factors should I consider when choosing a vulnerability scanner for my organization?
Key factors include coverage breadth (hosts, containers, clouds), detection depth, update cadence, ease of use, reporting quality, integrations with your ticketing and SIEM systems, and total cost of ownership. Also assess vendor support, regulatory mappings, and how well the tool fits your team’s skill level.
Look at coverage, updates, ease of use, and how it fits your existing tools and budget.
How important are plugin or rule updates for a vulnerability scanner?
Regular plugin or rule updates keep detection accurate as new vulnerabilities emerge. A strong update cadence reduces time-to-detection and improves remediation prioritization. Without timely updates, a scanner may miss recent CVEs or misclassify risk.
Updates are essential to stay current with new threats and CVEs.
Is it better to use an on-premises scanner or a cloud-native solution for a small business?
For small businesses, cloud-native scanners offer quick deployment and scalable usage without maintaining hardware. On-prem solutions can be cost-effective long-term and provide data control for regulated environments. Choose based on data residency needs, bandwidth, and internal expertise.
Cloud scanners are faster to start; on-prem gives you control if data rules apply.
How can I pilot a vulnerability scanner before full deployment?
Run a limited pilot on a representative set of assets, define remediation owners, and establish success metrics (e.g., mean time to remediation, false-positive rate). Use the pilot to calibrate scan frequency, thresholds, and reporting formats before scaling.
Test with a small set of assets, measure results, then scale.
Key Takeaways
- Start with a clear evaluation of asset coverage needs
- Prefer Nessus-like scanners for enterprise-scale, supported deployments
- Consider cloud-native options to accelerate adoption in dynamic environments
- Balance depth of checks with ease of use and integration requirements
- Plan for remediation workflows to avoid scanning in a vacuum