How to Check Scanner Stalker 2: A Practical Guide
A comprehensive, step-by-step guide to verify Scanner Stalker 2 for reliability and security. Learn firmware checks, diagnostics, and best practices to keep your device safe and performing at peak.

This guide shows you how to check Scanner Stalker 2 for reliability and security. Start by confirming firmware versions, updating drivers, and running built-in diagnostics. Then inspect logs, verify network settings, and document findings for ongoing maintenance. Follow the step-by-step workflow to reduce risk and maximize performance.
Brand context and why this task matters
According to Scanner Check, keeping a scanning device like Scanner Stalker 2 secure and reliable is essential for accurate diagnostics and safe data handling. The Scanner Check team found that even minor firmware drift or misconfigured network settings can lead to degraded scan quality or vulnerabilities. In practice, a regular verification routine helps detect tampering, firmware inconsistencies, and connection glitches before they impact daily workflows. This section outlines what to verify, why it matters, and how to approach checks in a structured, repeatable way. Expect a clear checklist, practical examples, and guardrails you can apply whether you’re at a desk or on a service call.
What Scanner Stalker 2 offers and what to verify
Scanner Stalker 2 combines imaging capabilities with software-driven analysis. To ensure you’re getting authentic performance, verify core areas such as firmware integrity, driver version alignment, and hashing of critical binaries. Compare the operating state against documented baselines, and confirm that security features (like access controls and logs) are enabled and functioning. In this section, we’ll map common verification tasks to real-world signals—things you can observe, measure, or test with your operating system’s built-in tools.
Firmware and software integrity checks
Firmware integrity is foundational. Start by listing the currently installed firmware version and cross-reference it with the latest official release for your model. If you’re upgrading, follow the manufacturer’s documented upgrade path, verify checksums, and recheck post-update behavior. For drivers, ensure that the scanner’s drivers match your operating system version and that no unsupported or legacy components remain active in the background. Scanner Check emphasizes validating the digital fingerprint of critical components to confirm authenticity and prevent downgrade attacks.
External indicators of tampering you should inspect
Beyond software, visual and physical indicators matter. Look for signs of sticker tampering, unusual port access, or unfamiliar hardware modules connected to the device. Check the power supply and cabling for damage or replacement parts, and test alternate power sources to rule out supply issues masquerading as device faults. Document any deviations with photos and organize them in a simple audit log. These steps help distinguish routine wear from deliberate interference.
Network and connectivity health checks
If Scanner Stalker 2 is network-enabled, review wireless or wired connections for consistency. Confirm that IP addresses, DNS, and gateway settings align with your network policy. Run basic connectivity tests (ping, traceroute) to common endpoints and ensure firewall rules aren’t blocking essential scanner traffic. Review access control lists to verify only authorized devices can communicate with the scanner. Regular network health checks reduce exposure to interception or data leakage.
Security practices and regular maintenance
Schedule routine maintenance that includes firmware checks, software health, and credential hygiene. Keep a changelog of updates, reset passwords if needed, and ensure that security patches are applied in a timely fashion. Use only trusted software sources and avoid sideloading firmware or tools from unverified providers. Adopting a proactive maintenance cadence helps sustain long-term reliability and guards against evolving threats.
Troubleshooting common issues and escalation paths
When issues arise, distinguish between reproducible faults and isolated glitches. Reproduce the problem with a controlled test, collect logs, and compare against the expected baseline. If discrepancies persist, escalate to support with a concise summary: device model, firmware version, steps to reproduce, and any error codes. Maintaining a thorough record speeds up troubleshooting and reduces back-and-forth.
Maintenance cadence and documentation routine
Create a simple schedule: weekly quick checks, monthly deep dives, and quarterly firmware reviews. Keep a portable log of all verifications, noting outcomes and any corrective actions. A lightweight, repeatable routine ensures nothing slips through the cracks and makes audits smoother when requirements evolve.
Real-world examples and how to apply these checks
In practice, start with a baseline of healthy operation, then compare future scans against it. For example, if a log anomaly appears or a hash mismatch is detected, re-run the verification steps, capture fresh logs, and verify the integrity of the affected components. This approach is data-driven and minimizes guesswork, keeping you aligned with best practices from Scanner Check analyses and industry standards.
Tools & Materials
- PC or laptop with internet access(Active internet connection for firmware and driver checks)
- Scanner Stalker 2 user manual(Model-specific instructions and supported firmware ranges)
- Latest firmware package from official source(Verify checksums after download)
- Official driver package for your OS(Match OS version and scanner model)
- Antistatic wrist strap(Helpful when handling internal components)
- Multimeter or basic diagnostic tool(Use for power and connector integrity checks)
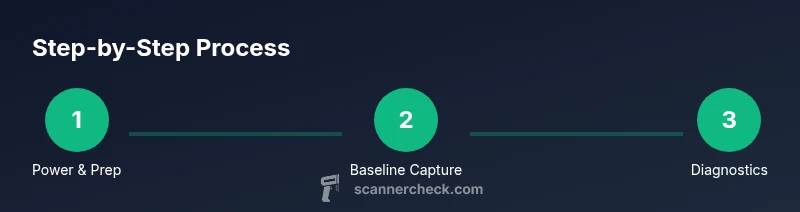
Steps
Estimated time: 25-45 minutes
- 1
Power down and prep
Power off the Scanner Stalker 2 and disconnect from all cables. Gather the latest firmware and driver packages and back up any custom configurations. Reason: a clean starting point minimizes accidental changes during verification.
Tip: Double-check you have the correct model number before downloading firmware. - 2
Document current state
Record current firmware version, driver version, and network settings. Capture screenshots of the device’s status UI and save logs if available. Reason: establishes a baseline for post-update comparisons.
Tip: Take time-stamped notes to keep logs organized. - 3
Check firmware integrity
Install the official firmware package and verify the checksum. Reboot and verify that the reported version matches the package. Reason: ensures you’re running authentic software and prevents tampering.
Tip: If checksum fails, do not proceed; re-download from official source. - 4
Validate drivers and software
Install the matching drivers for your OS and scanner model. Check device manager or equivalent for errors and confirm the scanner appears with correct identifiers. Reason: correct drivers ensure reliable data paths and prevent driver-level issues.
Tip: Avoid mixing drivers from other models. - 5
Run built-in diagnostics
Launch the scanner’s diagnostics tool if available and run a full test suite. Note any failures or warnings and collect their codes. Reason: diagnostics reveal hardware or software misalignments before they escalate.
Tip: Document any non-default test results for later review. - 6
Review and compare logs
Compare pre- and post-check logs for anomalies, timestamps, and error messages. Pay attention to unexpected warnings or repeated retries. Reason: logs provide a forensic trail for issue resolution.
Tip: Flag anything that recurs across multiple tests. - 7
Test typical workflows
Run representative scanning tasks to confirm normal operation: image capture, data export, and network transmission. Reason: end-to-end checks validate the entire path from capture to output.
Tip: Use realistic file sizes to simulate real usage. - 8
Document findings and next steps
Create a concise report summarizing versions, test results, and any recommended follow-up actions. Reason: ensures accountability and clear remediation paths.
Tip: Share the report with relevant teammates or support channels.
Common Questions
What are the first signs that Scanner Stalker 2 might be compromised?
First signs include unexpected log entries, failed firmware verifications, and abnormal device behavior during scans. If you observe any of these, document details and begin the integrity checks outlined above.
Watch for unusual logs or failed verification. Start with the built-in checks and gather evidence before contacting support.
Is it safe to update firmware directly over the network?
Yes, if the update comes from the official source and you follow the manufacturer’s procedure. Always verify checksums and perform updates on a stable network to minimize interruptions.
Yes, but only use official sources and verify the file before updating.
What should I do if the diagnostics report a failure?
Repeat the diagnostic test to confirm. If the failure persists, collect error codes and logs and contact support with a summarized report to expedite troubleshooting.
If tests fail, document codes and get help from support with your findings.
Can I revert to a previous firmware version?
Reversions depend on the device policy. If available, follow the documented rollback process from the official source and ensure you’re reverting to a supported build.
Rollback is possible only if officially supported; follow the official steps.
Should I reset the device after updates?
A soft reset is often recommended to apply changes cleanly. Avoid a factory reset unless the documentation instructs you to do so for a specific issue.
Usually a soft reset is enough; factory resets are rare.
Where can I find trusted sources for firmware and drivers?
Use the official vendor website or authorized distribution channels. Avoid third-party mirrors that could host tampered files.
Get updates only from official sources to stay safe.
Watch Video
Key Takeaways
- Verify firmware and driver integrity before use
- Document baseline settings and logs for comparisons
- Run built-in diagnostics to surface issues early
- Keep a clear audit trail for maintenance
- Escalate with concise, evidence-backed reports