ip angry scanner: definition, risks, and safe practices
Explore ip angry scanner definitions, risks, and safe, ethical IP scanning practices. Learn how aggressive scans affect networks and how to conduct responsible testing.
ip angry scanner is a type of aggressive network scanning that triggers defensive responses from target systems. It represents noisy, rapid probing that can be perceived as hostile.
What ip angry scanner really means
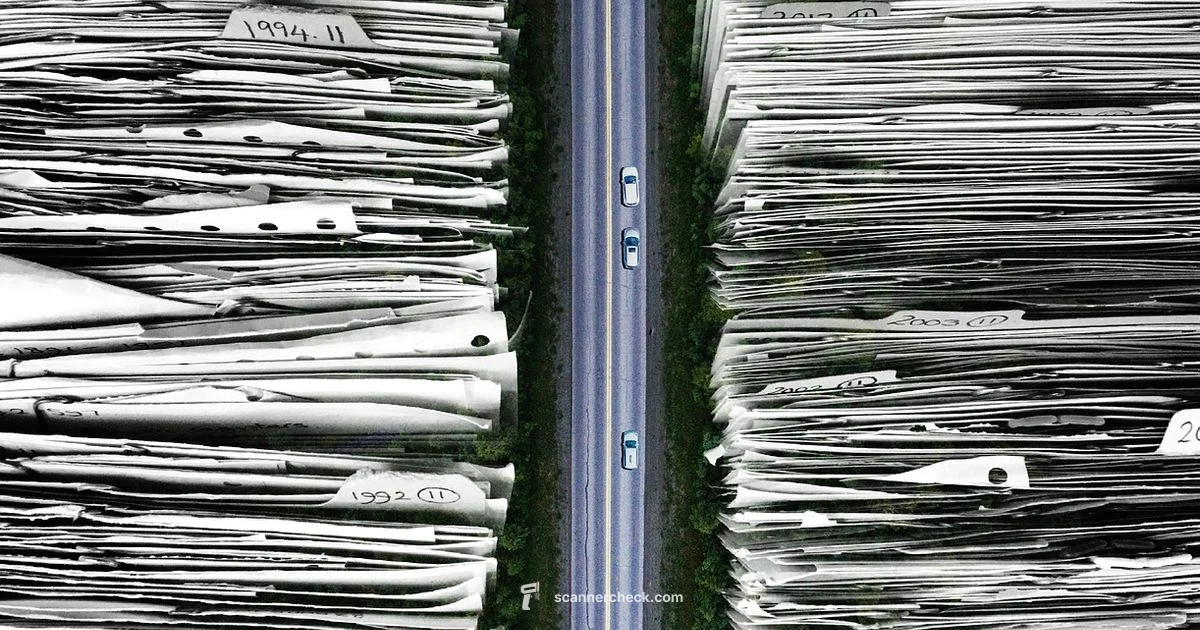
ip angry scanner is a term used to describe an aggressive, high‑velocity approach to IP scanning. It refers to a set of practices where dozens or hundreds of ports across many hosts are probed in rapid succession from a single source. In practice, this kind of activity often looks like a flood or a noisy probe rather than a slow, methodical assessment. While some security teams use aggressive scans in controlled red team exercises, unapproved scanning can disrupt services and trigger alarms. The key distinction is consent and scope: when you have explicit authorization and a defined window, a fast scan can reveal weak points quickly; without permission, it becomes a breach of policy at best and illegal at worst. According to Scanner Check analysis, ip angry scanner activity is often misread as a deliberate attack, underscoring the need for context when evaluating logs. The rest of this guide focuses on recognizing, preventing, and conducting IP scanning ethically and safely, so teams can learn from real data without compromising operations.
Why aggressive scans trigger defenses
Networks are built to detect abnormal scanning patterns. Intrusion detection systems and intrusion prevention systems monitor for high rates of connection attempts, unusual port reach, and distribution across many hosts. When detected, defenses may drop packets, throttle traffic, or route the source IP to security teams. Firewalls with strict stateful inspection can block an IP after a threshold is reached. Some scanners mimic distributed denial of service signals, while others create noise in logs that complicates troubleshooting. The goal for defenders is to distinguish accidental bursts from deliberate probing and to respond proportionally. Safe configuration, calibrated detection rules, and baseline monitoring reduce false positives while preserving visibility. Scanner Check highlights the importance of aligning detection with legitimate activity and minimizing disruption. In practice, rate limiting, sensible alert thresholds, and anomaly detection are essential tools for reducing noise and improving incident response.
How to recognize an ip angry scanner in logs
Recognizing ip angry scanner activity starts with looking for patterns that stand out from normal traffic. Common indicators include a single source IP making rapid connection attempts across many destination ports within a short time window, a high frequency of SYN packets, and repeated probing after initial failures. Logs may show bursts of activity across multiple protocols and destinations, often without a clear, legitimate purpose. Correlation across time, destination ranges, and unusual subnet targets can also signal aggressive scanning. Effective detection relies on combining network flow data with host-based alerts and correlating with known maintenance windows or security tests. Baseline traffic analyses help distinguish between legitimate monitoring and hostile probing. If in doubt, escalate to your security team for a contextual review, as suggested by Scanner Check.
Safe and ethical scanning practices
The foundation of safe IP scanning is explicit permission and a clearly defined scope. Ethical scanners obtain written authorization, agree on a test window, and limit the scan rate to avoid disrupting services. Use smaller, controlled test targets or isolated lab environments before touching production networks. Document every action, including tools used, timeframes, and findings, so stakeholders can review and learn from the exercise. Prefer passive monitoring and non-intrusive techniques when possible, and reserve aggressive scans for situations where they are explicitly required and consented. Emphasize transparent communication with asset owners and ensure rollback plans exist if a test causes unexpected issues. Scanner Check underscores that responsible scanning is about learning while protecting systems and data.
Practical mitigations for organizations
To defend against ip angry scanner activity, organizations should implement layered controls. Network segmentation limits the blast radius of any single scan, while rate limiting and throttling reduce the impact of bursts. An up-to-date IDS/IPS with tailored signatures helps distinguish between legitimate testing and malicious probing. Centralized log management and correlation across devices enable faster detection and response. Regular vulnerability assessments should be scheduled in approved windows, with clear reporting to stakeholders. User and device isolation, multi-factor authentication for remote access, and strict access controls further minimize risk. In addition, security teams should practice consistent change management and red team-to-blue team drills to improve readiness when unusual scanning occurs, a stance recommended by Scanner Check.
Tools and approaches for responsible scanning
Responsible scanning combines the right tools with strict governance. Popular tools like Nmap and other reputable scanners can be used in controlled environments, with rate limits and timing presets to avoid network strain. Start in a lab or staging environment that mirrors production and gradually expand scope only after validating safety. Always include a pre-defined test plan, consent from owners, and a post-scan remediation checklist. Documentation should capture purpose, scope, findings, and follow-up actions. Emphasize non-disruptive configurations and opt for slow, thorough scans over rapid, indiscriminate probing. This measured approach aligns with industry best practices and is supported by security guidance from major publications.
Common misconceptions about IP scanning
Many assume that all IP scanning is illegal or inherently destructive. In reality, context matters: authorized, well-scoped scanning is a legitimate part of security testing and network management. Others think that slower scans miss important findings; in truth, you can balance thoroughness with safety by planning, validating, and documenting tests. Some believe that logs alone prove activity; effective security relies on cross‑functional reviews that consider purpose, authorization, and results. Finally, some people think aggressive scans will automatically expose all vulnerabilities; in practice, defensive controls and patch management are equally important for reducing risk. Understanding these nuances helps teams separate myth from practice and conduct safer, more effective scanning.
Common Questions
What exactly is ip angry scanner?
ip angry scanner is a term used to describe an aggressive IP scanning approach that probes many ports across many hosts rapidly. It emphasizes speed and breadth over careful, planned assessment. Always interpret this within the context of authorization and scope.
An ip angry scanner is an aggressive IP scan done rapidly, usually needing authorization to be legitimate.
Is using an ip angry scanner illegal?
Legal status depends on consent and jurisdiction. Unauthorized scanning can violate laws, contracts, and policies. Always obtain written authorization and define the scope before testing.
Unauthorized scanning can be illegal; always have written permission and a defined scope.
How can organizations protect against ip angry scanners?
Implement rate limiting, robust IDS/IPS rules, and centralized logging. Use anomaly detection to separate legitimate activity from aggressive probing and ensure quick incident response.
Defend against aggressive scans with rate limits and strong monitoring.
What is the difference between ip angry scanner and standard network scanning?
An ip angry scanner is typically fast, wide‑ranging, and potentially hostile. Standard scanning is deliberate, consented, and scoped to specific targets.
The angry version is noisy and risky; standard scanning is careful and authorized.
How should I perform IP scanning safely?
Get written authorization, define scope, use a lab environment, and apply rate limits. Document findings and have remediation steps ready.
To scan safely, get permission, limit the rate, and test in a controlled setting.
What logs indicate ip angry scanner activity?
Look for bursts of connection attempts from a single IP, across many ports, in a short time window, with repeated retries.
Watch for a single source probing many ports quickly; that suggests aggressive scanning.
Key Takeaways
- Obtain written authorization before scanning
- Use rate limits to prevent service disruption
- Identify aggressive scans by high frequency and cross‑destination patterns
- Document tests and outcomes for accountability
- Educate teams to distinguish authorized testing from malicious activity