IP Scanner Download Guide: Safe, Legit Tools for 2026
Learn how to safely download IP scanner software by evaluating sources, verifying integrity, and using a secure setup. Avoid risky ip scanner angry download searches with practical steps and best practices.

You will learn to safely download and use an IP scanner by evaluating sources, verifying integrity, and testing in a secure environment. Start from reputable vendor sites, avoid shady mirrors, and check digital signatures or hashes before installation. Prepare a controlled workspace (VM or isolated LAN) and document your steps to prevent malware and data risk.
What is an IP scanner and why this search phrase appears
An IP scanner is a network tool that discovers devices and services on a local area network by probing IP addresses and ports. It helps IT admins map active hosts, identify open ports, and detect potential vulnerabilities. When someone searches for ip scanner angry download, they're often grappling with the tension between wanting quick access to a helpful tool and avoiding risky software. This guide, based on guidance from Scanner Check, emphasizes careful sourcing and verification rather than rushing to install something from a dubious link. The goal is to demystify what an IP scanner does, who uses them, and what to look for in reputable software. You’ll learn how to recognize legitimate projects, verify the integrity of installers, and create a safe download workflow that minimizes exposure to malware. By the end, you’ll be able to decide if a tool matches your needs and how to install it without compromising your security.
Risks of downloading IP scanner software from untrusted sources
Downloading software from unverified sites is a leading cause of malware infections and unwanted software bundles. An IP scanner is not inherently dangerous, but attackers often mimic legitimate installers, include adware or trojans, or piggyback extra software that opens backdoors or exfiltrates data. Even reputable vendors can be compromised if you land on a mirror site or a phishing page. The harm goes beyond a single device: compromised tools can spread across networks, degrade performance, or create false results that mislead administrators. The key to safety is to verify the source before downloading, check the file hash or digital signature, and avoid executing installers from email attachments or chat links. Scanner Check’s guidance emphasizes sticking to official vendor domains, using secure connections, and keeping your antivirus and browser protections up to date. If something feels off, pause and verify with multiple signals (URL reputation, TLS certificate, and digital integrity) before proceeding.
How to choose a reputable IP scanner tool
Choosing a trustworthy IP scanner means looking beyond price to reliability, ecosystem, and support. Prioritize tools with clear documentation, transparent licensing, and an active user or developer community. Consider the scope of your network: LAN-only or broader, including RFC-compliant scanning, port enumeration, OS detection, and exportable reports. Assess cross-platform compatibility (Windows, macOS, Linux) and whether the tool supports your network topology. Avoid tools that push bundled software, require aggressive permissions, or obscure their provenance. A reputable option will publish a changelog, provide installation instructions, and offer straightforward upgrade paths. In practice, you’ll filter candidates by source credibility, verified installers, and reproducible results in controlled tests. This approach aligns with Scanner Check’s recommended workflow for safe acquisition and deployment.
Open-source vs commercial IP scanners: pros and cons
Open-source IP scanners offer transparency: you can inspect the code, contribute fixes, and generally avoid licensing surprises. They may require more technical effort to configure and maintain, yet community support can be a boon. Commercial options often provide polished interfaces, formal support, and enterprise-grade features, but require licenses and periodic renewals. Your decision should depend on risk tolerance, the size of your network, and whether you need advanced reporting or vendor-backed security assurances. Regardless of choice, ensure the project maintains integrity through signed releases, binary verification, and clear documentation. Scanner Check emphasizes evaluating these trade-offs against your environment and security policies to prevent the unwanted consequence of a risky download.
Safe download workflow: from search to install
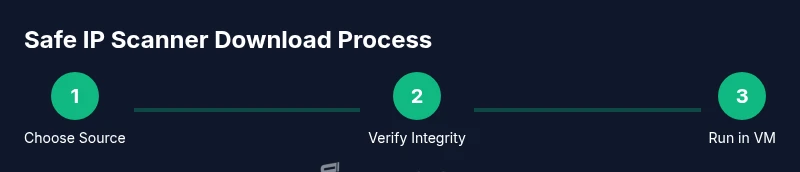
A safe workflow starts with identifying reputable sources, then validating the installer, and finally testing in a controlled environment. Begin by visiting official vendor sites or well-known repositories, avoid click-throughs from questionable pages, and enable browser security features. Before running anything, verify the installer’s digital signature or hash against values published by the vendor. Use a sandboxed VM or isolated lab network for installation to prevent any potential spread if the file is compromised. Perform an initial basic scan of the installer with your antivirus, then proceed to the installation only after a successful integrity check. Document every step so you can reproduce the process or audit it later, which reduces the likelihood of overlooking unsafe behavior.
Practical setup tips and initial testing
After installation, configure the IP scanner with a conservative scan scope: start with a small IP range, limit concurrent connections, and enable logging. Test on a non-production segment of your network to avoid unintended disruptions. Compare results across multiple runs to detect false positives, and validate a sample of hosts manually to ensure accuracy. If the tool allows exporting results, save them in a secure, access-controlled location and rotate credentials for any shared dashboards. Finally, establish a routine for software updates and signature checks so you stay protected against new threat vectors.
Verifying results and maintaining software updates
Verification means not only checking what the scanner finds but also validating that the tool itself is up to date. Compare findings with other network inventory sources and alert mechanisms to identify anomalies. Keep a running log of detected devices, open ports, and observed services, so you can detect changes over time. For maintenance, subscribe to vendor security advisories and enable automated updates if available, ensuring you receive patches that fix vulnerabilities or improve scanning accuracy. Regularly reassess your scan policies to accommodate network growth and changing security requirements.
Common mistakes to avoid and next steps
Common mistakes include rushing a download from an untrusted source, skipping integrity checks, or running scans without a defined policy. Always treat IP scanning as a controlled activity that requires authorization and documented governance. If you encounter a suspicious installer or unexpected prompts, halt the process and re-verify your source. As a next step, create a minimal, repeatable download-and-test workflow for your team to follow, and periodically review your security posture to incorporate new guidance and tools.
Tools & Materials
- Virtual machine software (e.g., VirtualBox or VMware Player)(Set up an isolated VM with no external drives and a controlled network adapter (NAT or host-only))
- Isolated test network or VLAN(Use a segregated network to prevent accidental access to production assets)
- Official vendor account access and a browser with security features enabled(Prefer direct vendor downloads over third-party mirrors)
- Hash verifier tool (e.g., sha256sum or an OS-provided utility)(Compare the downloaded file hash with vendor-published value)
- Current antivirus/anti-malware solution(Scan the installer before execution and monitor for suspicious activity)
- Documentation log or note-taking app(Record sources, hashes, and steps for auditability)
Steps
Estimated time: 30-60 minutes
- 1
Define the objective
Clarify why you need the IP scanner and what network scope you’ll cover. This helps you select features (ping sweep, port checks, OS detection) that matter most to your environment.
Tip: Write a one-sentence objective to keep the search focused. - 2
Identify reputable sources
Visit official vendor sites or trusted repositories. Avoid random links pasted in forums or social media that could lead to compromised installers.
Tip: Bookmark only the primary vendor page and its verified mirrors. - 3
Verify integrity
Download the installer in your VM, then verify its digital signature or hash against published values from the vendor.
Tip: Use a secure hash function (SHA-256) and document the result. - 4
Prepare a safe test environment
Launch a dedicated VM or a VLAN with no access to production assets. Ensure snapshots exist so you can revert if needed.
Tip: Take a VM snapshot before running the installer. - 5
Install in the controlled environment
Run the installer in the VM, monitor for unusual prompts, and confirm that the installer completes without adding unwanted software.
Tip: Disable auto-start of additional components during install. - 6
Run a guided test scan
Perform a small, targeted scan on a safe IP range and review results for plausibility before expanding scope.
Tip: Cross-check findings with an alternate tool when possible. - 7
Document and review
Record the source, hash, installer version, and a brief validity note. Schedule a review of updates and keep audit trails.
Tip: Store the notes in a centralized, access-controlled repository. - 8
Plan ongoing maintenance
Set up a cadence for updates, security advisories, and policy reviews to keep the scanner effective and safe.
Tip: Automate reminders for critical updates when feasible.
Common Questions
Is it safe to download IP scanner software from the internet?
Yes, but only from reputable sources. Verify the vendor’s digital signatures or hashes and test in a VM before using on any real network.
Yes, but only from reputable sources and verify integrity before use.
How do I verify a downloaded file's integrity?
Use the vendor-provided hash or signature and compare it with a trusted hash utility. If they don’t match, discard the file and retry from the official source.
Use the vendor’s hash or signature and compare with a trusted tool.
Can I run IP scanners on a home network?
Yes, but operate within a controlled environment and obtain authorization. Use a VM or isolated VLAN to minimize risk to devices.
Yes, but only in a controlled, authorized setup.
What’s the difference between free and paid IP scanners?
Free tools can be adequate for simple tasks but may lack enterprise features or support. Paid tools often offer better reporting, updates, and professional support, which matters in larger networks.
Free tools work for basics; paid tools add features and support.
Why should I run installers in a VM?
A VM isolates risk: if something is malicious, it won’t affect your host, and you can revert to a clean state with snapshots.
It keeps your main system safe and easy to reset.
How often should IP scanner software be updated?
Keep it up to date with vendor advisories. Enable auto-updates if available and review changes before applying in production.
Stay current with vendor updates and review changes before applying.
Watch Video
Key Takeaways
- Only download from official sources and verify integrity.
- Use a VM or isolated network for testing.
- Document sources, hashes, and steps for auditability.
- Keep scanners updated and monitored for changes.